A few of our recent articles have taken us into the realm of NFTs, but we’ve primarily kept to the basics. One less-highlighted aspect of NFTs is that they’re built upon smart contracts, and smart contracts can be exploited, broken, and hacked. Similar to any typical DeFi project with imperfect smart contracts, NFT smart contracts can carry vulnerabilities that lead to unfavorable outcomes. We’ll go over what people have done over the years to exploit NFT contracts, as we discuss the history and a few unfortunate mishaps that lead to funds being lost.
CryptoPunks
Arguably the most popular NFT project to date, CryptoPunks had an impactful bug in their smart contracts after launching in 2017. After all 10,000 Punks were sold and the secondary market kicked off, a bug was discovered where sales could occur but no actual payment was received.
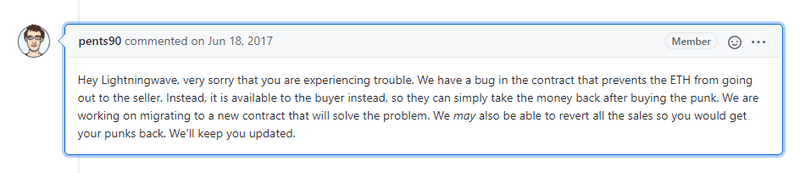
The issue in the code came down to one line - it wasn’t tested enough to be ready. @0xfoobar later published a Twitter thread that thoroughly explained the bug.
LarvaLabs, the creators of CryptoPunks, ended up re-launching the project with a new, updated contract. The V1 punks that were part of the original contract were mostly forgotten until a V1 CryptoPunks ERC-721 wrapper was released, which also dubbed the V1 punks as “ClassicPunks.”
Meebits
Years after launching CryptoPunks, LarvaLabs launched a follow up project called Meebits. All Meebits were minted with random traits. However, when launched, a few users figured out how to cheat the system and re-roll traits to get the ones they wanted.
How? The Meebits project had an archived file included in the smart contract that showed the characteristics of each Meebit token ID. Users could initiate the minting of a Meebit and then cancel it if they saw that the token was not rare by comparing the file of traits. One user took full advantage of this and publicly documented his success on Twitter and Discord. The user in question is ‘0xNietzsche.’
0xNietzsche initiated more than 300 transactions to test out this exploit. Every Meebit they initiated the minting for was canceled if it didn’t have rare enough traits. After 300+ transactions, they finally were able to stumble upon a rare Meebit, #16647.

0xNietzsche claimed they had spent $20,000 per hour in gas fees waiting to mint their rare Meebit, but they had nonetheless exploited the contract to do so. They were able to sell their newly minted Meebit for 200 ETH, which was valued at around $750,000 USD at the time.
LarvaLabs got wind of this shortly after and temporarily halted the Meebit minting, issuing the statement, “We have temporarily paused community minting and trading in the Meebits contract. The contract is safe, all Meebits are safe, and trading is working just fine.” They were correct, Meebits were still assigned completely at random - and you couldn’t exploit the contract unless you put a lot of time and gas fees into it, and at that point, the minting was nearly all finished anyway.
Nonetheless, Meebits is a very good example of how a smart contract was exploited to allow one or more users a competitive advantage when minting NFTs.
6/ Should Meebit owners be worried?
— Sillytuna 💯 (@sillytuna) May 8, 2021
No, it wasn't possible to mint arbitrarily, this was a way to select the final rare meebits, of which they got one.
This is now just part of the Meebit story. Embrace it. pic.twitter.com/SSc4V0gY6M
MoonCatRescue
MoonCatRescue launched in 2017 and right off the bat had a pretty big flaw in their contract.
The MoonCats Official FAQs page asks the question: Are you getting paid for this?
The reply:
“Nope. We intended to collect ether from the sale of the genesis cats. As it turns out however, a fix we made during our QA process led to those funds being locked away forever. But that is okay.”
When the MoonCat was adopted ```transferCat(catId, catOwners[catId], msg.sender, offer.price), the funds are sent to ```require(catOwners[catId] != 0x0. Double checking that it works in testing would have solved this issue. While it’s not a major flaw in smart contracts, they still lost out on a fair amount of ETH before they realized the error.
See more here: https://etherscan.io/address/0x60cd862c9c687a9de49aecdc3a99b74a4fc54ab6#code
Vulnerabilities in Smart Contracts as a Whole
In March 2018, five Computer Scientists collaborated on a paper titled, ‘Finding The Greedy, Prodigal, and Suicidal Contracts at Scale,’ for which they examined:
- Greedy Contracts, which lock funds indefinitely
- Prodigal Contracts, which leak funds carelessly to arbitrary users
- Suicidal Contracts, which can be killed by anyone
They went through close to 1 million (970,898) smart contracts on the Ethereum Network. Of these, they found 34,200 to be vulnerable to hacking/exploitation, meaning that in 2018, roughly 1 in 20 smart contracts were at risk. They went deeper and analyzed 3,759 contracts to concretely validate that they had flaws within their code, finding that 3,686 showed vulnerabilities that were all uncovered within an average time of 10 seconds per contract. That’s crazy! The maximum amount of Ether that they could have withdrawn from contracts is 4,905 ETH - which is a little over $8.6 million. The report also added, “In addition, 6,239 Ether (about $5.6 million) is locked inside posthumous contracts currently on the blockchain, of which 313 Ether have been sent to dead contracts after they have been killed.” That is a lot of crypto just stuck inside dead contracts. At the time this study was conducted, DeFi and other smart contracts accounted for far less on-chain activity. Flash forward to a more recent report published by Glassnode on May 6th, 2021, found that 22.8% of circulating ETH was locked in smart contracts.
#Ethereum supply dynamics tell a compelling story for the future for the protocol.$ETH on exchanges falls to 12.0% of circ. supply, as$ETH in smart contracts rises to 22.8%.
— glassnode (@glassnode) May 6, 2021
Our Analysis: https://t.co/0aSkAg1j04
Live Chart: https://t.co/UNF8PcisKS pic.twitter.com/g0P08haMiY
Is it still the case that 1 in 20 smart contracts are vulnerable to attacks? Have projects gotten safer or, as smart contracts become easier for people with little knowledge to publish, maybe the situation has gotten worse? Even if we kept the 1 in 20 ratio, that would mean that approximately 1% of all ETH in supply is in a vulnerable smart contract.
The takeaway here is to do your research before jumping into a project. Try not to FOMO. Make sure the project you want to invest in spent time developing the smart contract, and that this project didn’t spring out of nothing. A lot of copy-pasted code lives out there, and that’s always a red flag.